Information And Cyber Security Policy To Protect You
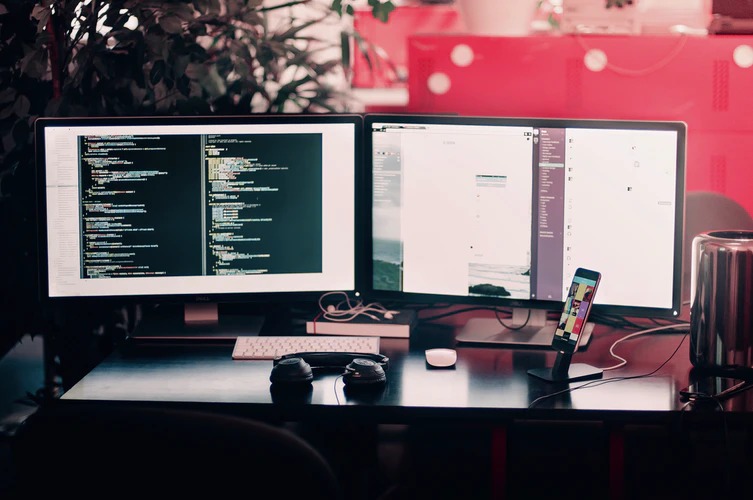
Information And Cyber Security Policy To Protect You. Would you want to guard yourself against malware, e-mail, and social engineering attacks? See our free defense models library below. What Is A Security Policy? Information management controls all data flows in an enterprise. While cybersecurity policies focus on automated data safety. A security strategy is a […]
Information And Cyber Security Policy To Protect You Read More »